- Solution 1: Code Level
- Solution 2: System Level
- Update patch KB3140245
- Enable TLS 1.1 and 1.2 at the SChannel component level on Windows 7 (using any of the following updates).
- Method 1: Update MicrosoftEasyFix51044.msi using the Microsoft Update installer.
- Method 2: Manually update the registry
- WIN7 64
- Windows Server
- Verify whether the system supports TLS 1.2 and TLS 1.3.
- Solution 3: Upgrade the system
- Other reference materials
- Other reference materials 1
- Other Reference Content 2
- The installed updates include
- Other reference content three
- Supplementary information
Description: Request aborted: Could not create SSL/TLS secure channel. Platforms affected: Windows Server 2012, Windows 7 Service Pack 1 (SP1), and Windows Server 2008 R2 SP1
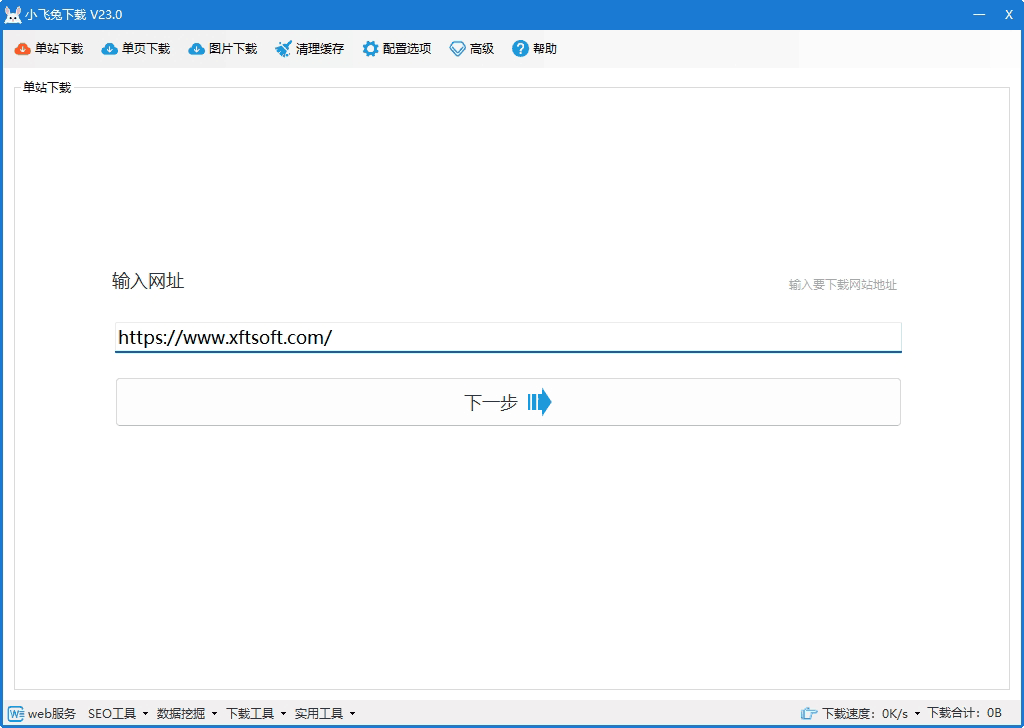
[episode] Download the whole site This is a website download tool. Simply enter the URL to download with one click. It's simple and easy to use, and supports multi-threaded tasks.
Solution 1: Code Level
Set code before HttpWebRequest
ServicePointManager.Expect100Continue = true; ServicePointManager.SecurityProtocol = SecurityProtocolType.Tls12 | SecurityProtocolType.Tls11 | SecurityProtocolType.Tls; ServicePointManager.ServerCertificateValidationCallback = (sender, certificate, chain, errors) => true;
Solution 2: System Level
If the above methods don't work, then the problem is at the system level. Check your current system for updates and patches.
This update enables TLS 1.1 and TLS 1.2 as the default security protocols in WinHTTP in Windows. This update provides support for Transport Layer Security (TLS) 1.1 and TLS 1.2 in Windows Server 2012, Windows 7 Service Pack 1 (SP1), and Windows Server 2008 R2 SP1. Refer to the official documentation. https://support.microsoft.com/en-us/help/3140245/update-to-enable-tls-1-1-and-tls-1-2-as-default-secure-protocols-in-wi
Update patch KB3140245
Enable TLS 1.1 and 1.2 at the SChannel component level on Windows 7 (using any of the following updates).
Method 1: Update MicrosoftEasyFix51044.msi using the Microsoft Update installer.
- Microsoft installs and updates the registry:http://download.microsoft.com/download/0/6/5/0658B1A7-6D2E-474F-BC2C-D69E5B9E9A68/MicrosoftEasyFix51044.msi
Method 2: Manually update the registry
Copy the registry code below and import it into the registry. Create a new text file, change the .txt extension to .reg (registry key), and import it (make a backup before importing).
WIN7 64
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\WinHttp] "DefaultSecureProtocols"=dword:00000a00 [HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Internet Settings\WinHttp] "DefaultSecureProtocols"=dword:00000a00 [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings] "SecureProtocols"=dword:00000a80 [HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings] "SecureProtocols"=dword:00000a80
Windows Server
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\WinHttp] "DefaultSecureProtocols"=dword:00000800 [HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Internet Settings\WinHttp] "DefaultSecureProtocols"=dword:00000800 [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.1\Client] "DisabledByDefault"=dword:00000000 "Enabled"=dword:00000001 [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.1\Server] "DisabledByDefault"=dword:00000000 "Enabled"=dword:00000001 [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client] "DisabledByDefault"=dword:00000000 "Enabled"=dword:00000001 [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Server] "DisabledByDefault"=dword:00000000 "Enabled"=dword:00000001
Verify whether the system supports TLS 1.2 and TLS 1.3.
Open with PowerShell:
[Net.ServicePointManager]::SecurityProtocol [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Ssl3 -bor [Net.SecurityProtocolType]::Tls -bor [Net.SecurityProtocolType]::Tls11 -bor [Net.SecurityProtocolType]::Tls12 -bor [Net.SecurityProtocolType]::Tls13
The first line of code checks the supported TLS version; the second line of code modifies TLS support.
Solution 3: Upgrade the system
If the first two methods don't work, we have to use the ultimate solution:
- Upgrade your system to Windows 10 and Windows Server 2019 (supports TLS 1.2);
- Upgrade your system to Windows 11 and Windows Server 2022 (supports TLS 1.3).
Note: For details on the TSL versions supported by each Windows version, please refer to the supplementary information section of this article.
Other reference materials
Other reference materials 1
Solutions exist, but they depend on the framework version:
.NET 4.6 and later. You do not need to do any additional work to support TLS 1.2, which is supported by default.
.NET 4.5 supports TLS 1.2, but it is not the default protocol. You need to choose to use it. The following code sets TLS 1.2 as the default; please ensure it is executed before connecting to secure resources:
ServicePointManager.SecurityProtocol = SecurityProtocolType.Tls12
.NET 4.0 does not support TLS 1.2. However, if .NET 4.5 (or later) is installed on your system, you can still choose to use TLS 1.2 even if your application framework does not support it. The only issue is that .NET 4.0's SecurityProtocolType does not have an entry for TLS 1.2, so we must use the numeric representation of this enumeration value:
ServicePointManager.SecurityProtocol =(SecurityProtocolType)3072;
.NET 3.5 or earlier. TLS 1.2 is not supported (*), and there is no workaround. Upgrade your application to the latest version of the framework.
PS: For scenario 3, there's also a registry hack that forces .NET 4.5 to use TLS 1.2 by default, without requiring programmatic enforcement. PPS: As Microsoft's Christian Pop mentions below, .NET 3.5 has a recent patch that enables TLS 1.2 support.
Please see:
- KB3154518 – Reliability Rollup HR-1605 – NDP 2.0 SP2 – Win7 SP1/Win 2008 R2 SP1
- KB3154519 – Reliability Rollup HR-1605 – NDP 2.0 SP2 – Win8 RTM/Win 2012 RTM
- KB3154520 – Reliability Rollup HR-1605 – NDP 2.0 SP2 – Win8.1RTM/Win 2012 R2 RTM
- KB3156421 -1605 HotFix Rollup through Windows Update for Windows 10.
Other Reference Content 2
The website may be providing a certificate key that is 512 bits long, while current industry standards require a public key of at least 2048 bits. Microsoft addressed this issue in a September 2016 security update, stating that if the public key length is less than 2048 bytes (e.g., RSA 512), it should be correct.Windows can disable HTTPS connections.
The installed updates include
2012 R2 and Windows 8
- KB3185331
- KB3188743
- KB3174644
2008 R2 and Windows 7
- KB3185278
- KB3185330
- KB3192391
- KB3175024
- KB3172605
Other reference content three
SecurityProtocolType.Tls1.0=0xC0; SecurityProtocolType.Tls1.1=0x300; SecurityProtocolType.Tls1.2=0xC00;
.NET 4.0/4.5 default values: SecurityProtocolType.Tls | SecurityProtocolType.Ssl3 .NET 4.6/4.7 default values: SecurityProtocolType.Tls | SecurityProtocolType.Tls11 | SecurityProtocolType.Tls12
The `SCH_USE_STRONG_CRYPTO` flag will be used automatically in .NET Framework 4.6. https://support.microsoft.com/en-us/help/3154518/support-for-tls-system-default-versions-included-in-the-net-framework TLS 1.2 is supported in Win7 SP1 and .NET 3.5.1.
ServicePointManager.SecurityProtocol &= ~SecurityProtocolType.Ssl3; // Disable SSL3 ServicePointManager.SecurityProtocol |= (SecurityProtocolType)0x300 | (SecurityProtocolType)0xc00; // Add support for SSL3 and SSL3
The conclusion of TLS 1.2 is as follows:
- Installing .NET 3.5.1 requires a patch to add TLS 1.2 enumeration.
- Installing .NET 4.0 requires modifying the registry and then adding the TLS 1.2 enumeration.
- After installing .NET 4.5, you also need to add TLS 1.2 enumeration.
- After installing .NET 4.6.1, TLS 1.2 is supported by default.
Registry modification under .NET 4
Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\.NETFramework\v4.0.30319] "SchUseStrongCrypto"=dword:00000001 [HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\.NETFramework\v4.0.30319] "SchUseStrongCrypto"=dword:00000001
Supplementary information
- The following supplementary and compiled articles:Windows version of TLS protocol supported in TLS/SSL (Schannel SSP)
This article is byDownload the whole siteThis content was compiled and edited from the internet. Please indicate the source when reprinting. Thank you.